Learn what Role-Based Access Control (RBAC) is and how Orkes Conductor uses RBAC to secure workflows, prevent unauthorized access, and keep your automations safe.
I love a superb scary story, especially during this season, but there is fun scary and then there is I-have-actual-nightmares-for-weeks-and-all-the-dogs-die-in-the-movie scary.
Your workflows without proper security? Definitely the second kind.
And you know that classic horror scene where someone clearly shouldn’t go into the dark basement, yet no matter how loudly you yell “Don’t go in there!”... they go anyway? If only something could stop them.
That’s where RBAC comes in. They keep your users and workflows from making that same bad decision.
If you're not familiar with RBAC, I'm glad you're here, I will start by going over that real quick. And if you already know the basics and just want to see how Orkes Conductor handles it, feel free to skip ahead.
What is RBAC?
RBAC stands for Role-Based Access Control. You’ve probably heard the term when people talk about security or authentication.
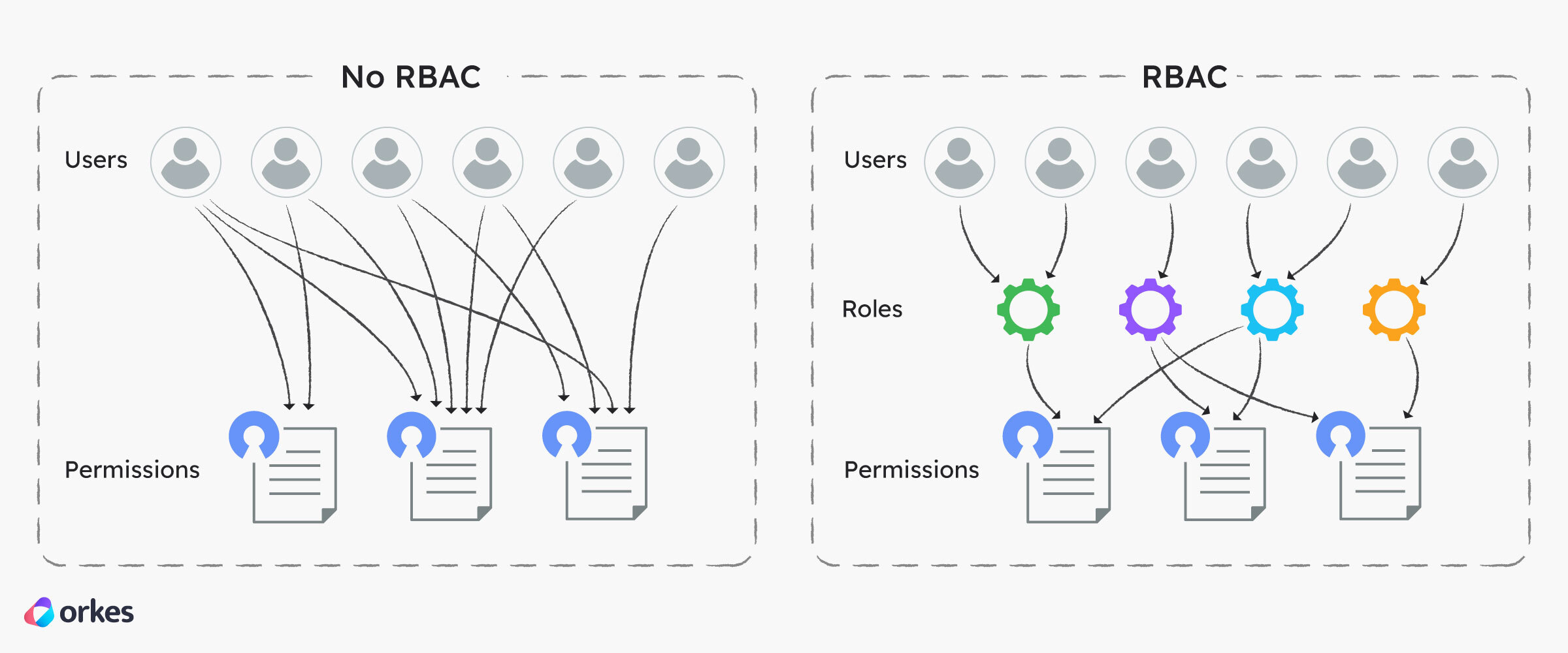
It's a system for controlling who can do what in your app, system, or workflow, based on their role rather than their individual identity.
This means that instead of giving permissions to every single user one by one, you assign permissions to roles (like “messenger,” “approver,” or “data syncer.” Or "entry level employee", "mid level employee", "high level employee") Then you simply assign users (or ghosts 👻) to those roles.
If a ghost’s role only allows them to enter the Send Messages house, they can’t sneak into the Approve Requests or Sync Data ones. They'll be denied access. How convenient.
The nightmares that happen without RBAC?
Not to scare you too much, but here are some terrifying things that can happen to your workflows without proper RBAC:
- 🎃 Anyone can change critical workflows. Without role-based permissions, even users who shouldn't have edit access might modify production workflows.
- 🎃 Production chaos disguised as testing. When environments share permissions, test changes can accidentally run in production. (Just thinking about it gives me goosebumps.)
- 🎃 Secrets slip through the cracks. Users or services without proper restrictions might access credentials or API keys they shouldn’t see.
- 🎃 Duplicate or runaway workflows. Without clear ownership, people might trigger the same workflow multiple times or create conflicting versions.
- 🎃 No trace of who did that. If everyone has the same level of access, it’s almost impossible to audit changes or identify the source of issues.
In short, without RBAC, your orchestrations turn into the not-so-fun nightmares. You get unauthorized edits, runaway executions, and production systems haunted by “unknown users.”
RBAC acts as your protective ward, defining who can create, edit, run, and observe workflows so your automation realm stays stable, secure, and completely un-haunted.
So how does RBAC work (technically)?
Behind the scenes, RBAC connects three key elements, users, roles, and permissions, to define exactly who can do what inside your system or workflow.
- Users — Real people, services, or systems that take action. A user might be a developer logging into the Orkes Conductor UI, a Slack bot calling a Conductor API, or a microservice triggering an event.
- Roles — Sets of permissions defining what actions a user or service can take (e.g., who can run, edit, or view workflows). When someone’s responsibilities change, you simply switch their role instead of manually updating every permission
- Permissions — The specific actions allowed within the system (like starting workflows, editing definitions, or viewing execution logs).
When a user (or service) tries to perform an action, the system checks their assigned role and verifies whether that role has permission to do it. If yes, the action proceeds. If not — access denied.
How Orkes Conductor’s RBAC protects your workflows
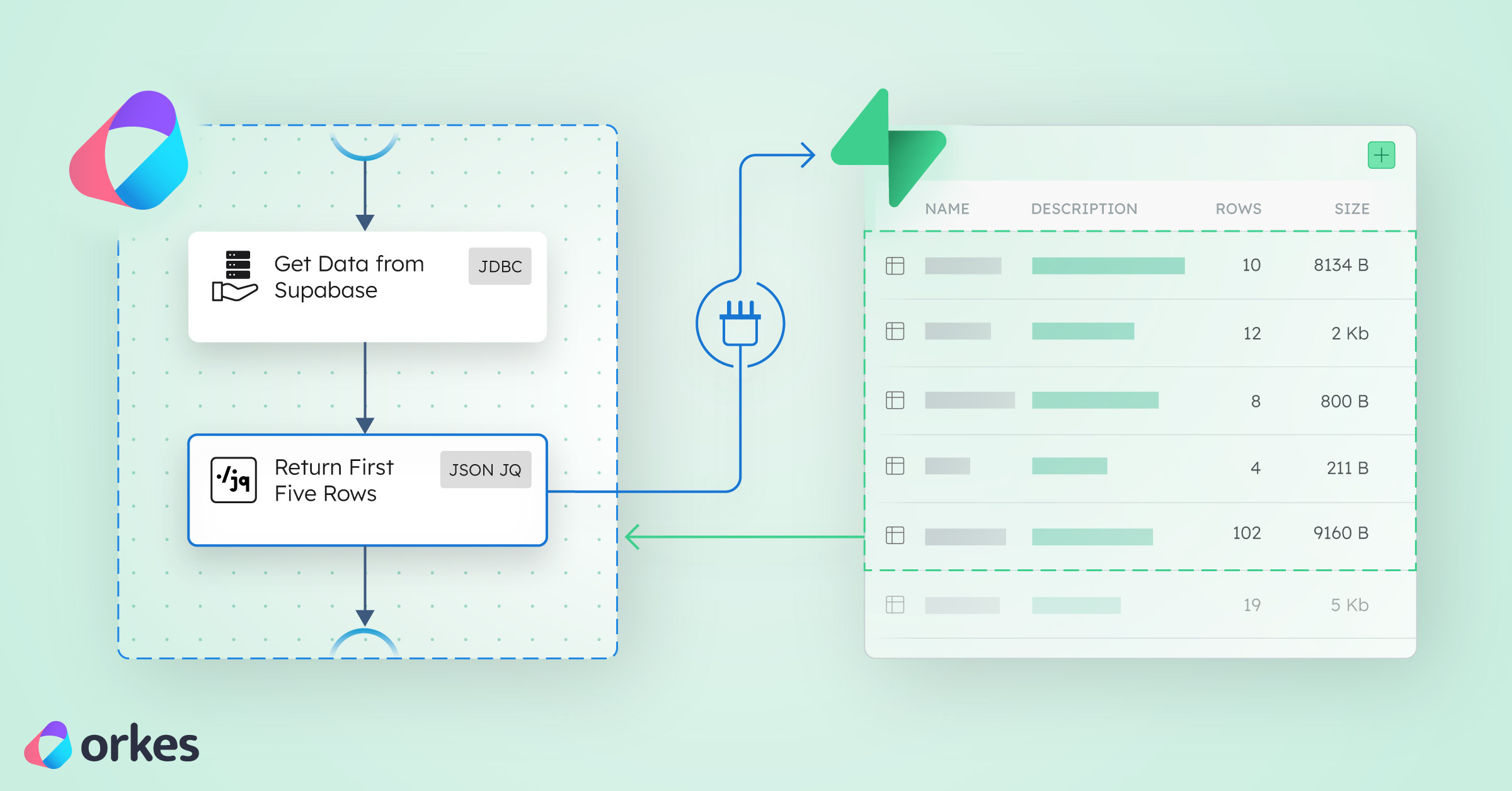
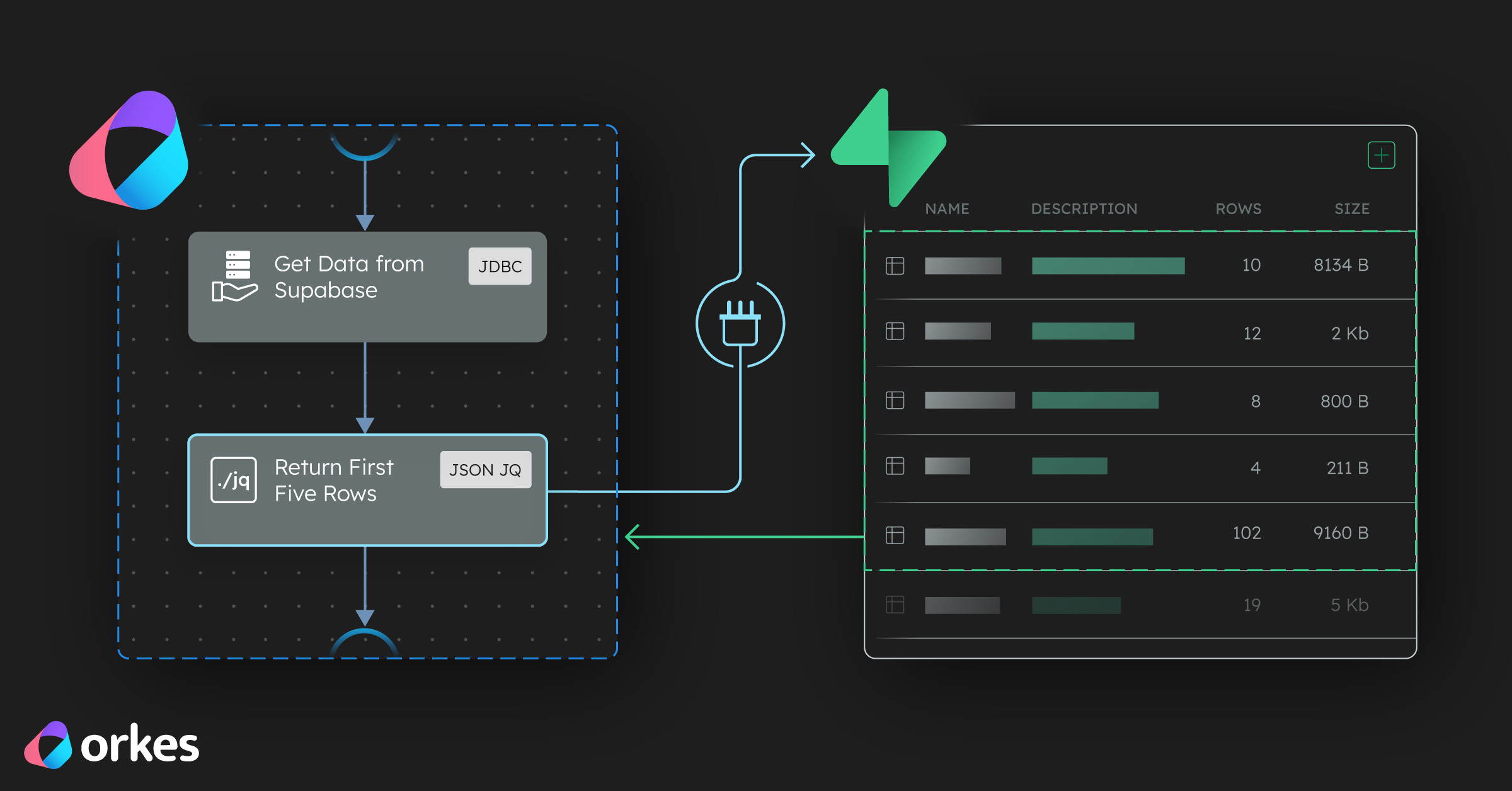
Orkes Conductor provides Role-Based Access Control (RBAC) for both individual users and applications that interact with its API and SDKs.
What this means is that you can define and enforce fine-grained permissions to control who can access specific workflows, tasks, or resources, and what actions they’re allowed to perform (such as viewing, executing, or modifying them based on their assigned roles.)
There are a ton of fun and diverse ways you can play around with permissions to fit your exact situation.
Applications, Groups, and Users
When you log into your Orkes Conductor account, you’ll find an Access Control tab on the left-hand side. Inside, you’ll see Applications, Groups, and Users.
- Applications: Create non-human identities (like bots, scripts, or services) that interact with Conductor. Each application only gets the permissions it needs — following the principle of least privilege. No need to share more than you have to.
- Groups: Organize users who share similar roles or responsibilities. Managing permissions at the group level ensures everyone gets the right access automatically.
- Users: Add individual human users and assign them roles and groups. What this mean in terms of RBAC is that each user can only see and do what their assigned roles and groups allow. In other words, RBAC makes sure every person has just the right amount of access they need to do their work
Roles and Tags
Orkes Conductor’s Roles and Tags make RBAC management flexible and scalable.
- **Roles: These are like permission bundles. They define what actions someone or something can do in Conductor. You can assign roles to users, groups, or applications. For example, a User role might allow someone to create and run their own workflows, while a Workflow Manager role might also let them view and manage all workflows in the cluster.
- Tags: Tags make it simple to manage permissions across multiple workflows or tasks. A tag is a small label (a key-value pair) you can add to any resource, like
env:staging or team:payments. When you give access to a tag, that access applies to all resources with the same tag. So instead of manually granting permissions for each workflow, you can tag related ones and manage them all at once.
A Real-World Example: Protecting a Developer Workflow
Let’s see what this looks like in action.
Imagine you’re a developer building an internal deployment automation using Conductor.
Here’s your simple workflow:
- Build the API service — package up your latest code.
- Run integration tests — verify that everything plays nicely together.
- Deploy to staging — test it in a safe environment.
- Trigger the production deployment — after all checks pass.
- Send a Slack notification — to celebrate the successful release.
With Orkes Conductor’s RBAC, you can lock down your deployment process so only the right people and services can change or trigger it.
For example, you can create a Developers group and give them permission to edit and test workflows only in the staging environment. Nowhere near production.
Your Release Manager can have a role that allows them to deploy to production.
Your CI/CD application can use an application account with just enough access to run builds and execute tasks, but not to edit or delete anything.
You can also add tags like env:staging and env:prod to your workflows, tasks, and secrets. By granting access to these tags instead of individual resources, you can control who touches staging versus production with just a few clicks.
And if something ever does go wrong, Conductor’s audit trail lets you see exactly who ran what and when.
Final Thoughts
Together, these RBAC tools create a clear boundary between testing and production, keep sensitive data safe, and make sure every action in your workflow happens for the right reason, by the right person (or bot).
So next time you build your automation, let RBAC be your shield.
Give power only to the worthy, keep your workflows safe from chaos, and rest easy knowing your orchestration realm is free from the wrong type of scary.